With the development of computing technology, we have entered the network era from the PC era, and then entered the post-PC era. IBM created a term in 1999 - "ubiquitous computing" (also known as "popular computing", Pervasive CompuTIng). “Universal computing†means “anywhere, whenever you need it, you can access the information you need through a deviceâ€. From the perspective of computing technology, humans have gradually extended from network computing to ubiquitous computing.
In general, ubiquitous computing has a wide range of meanings, including mobile communication technology, small computing device manufacturing technology, operating system technology and software technology on small computing devices. Pervasive computing is a ubiquitous way to perform calculations anytime, anywhere; mainly for mobile devices, such as information appliances or some kind of embedded devices, such as handheld computers, BP machines, car smart devices, notebook computers, watches, smart cards A new generation of smart devices such as smartphones (with some features of handheld computers), set-top boxes, POS vending machines, and screen phones (in addition to the functions of ordinary phones, you can also browse the Internet). Pervasive computing devices can be connected to the network either continuously or intermittently. Connected to the Internet, Intranet and Extranet, enabling users to access and respond to relevant information anytime, anywhere. Due to the high mobility of ubiquitous computing devices, it is also known as mobile computing. Pervasive computing provides access to back-end data, applications, and services over a network using a variety of ubiquitous computing devices. No matter which ubiquitous computing device is used, users will have easy access to information and services. Pervasive computing reduces the complexity of device use and helps improve the efficiency of outside work and the level of everyday life of people.
From the perspective of software systems, ubiquitous computing refers to the use of small computing devices, in the process of continuous location movement or in a wide geographical distribution, to achieve online transaction processing and enterprise core under unstable communication conditions. data access. These small computing devices have a variety of communication means, such as mobile communication networks, satellites, etc., which can be connected to the Internet or an intranet, but such connections are not fixed connections, but intermittent connections. Pervasive computing software technology allows users to use these devices for complex online transaction processing and information access because the devices used by users are small and the available computing resources (memory, storage, and CPU) are quite limited, most of the processing Work is done by the data center and application server of the computing center.
The rapid spread of Internet and network applications and the expansion of the family field, the trend of integration of consumer electronics, computers, communications (3C) is becoming more and more obvious; the advent of the information age, the embedded system is increasingly concerned by the market and manufacturers, embedded The increasing popularity of devices has also contributed to the development of ubiquitous computing.
1 embedded system
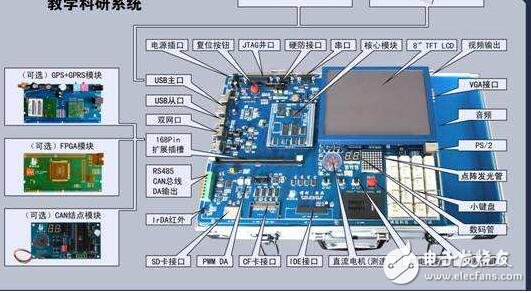
Embedded system is a dedicated computer system with embedded computer as the core of technology, user-oriented, product-oriented, application-oriented, software and hardware can be reduced, suitable for comprehensive requirements of function, reliability, cost, volume, power consumption, etc. . Unlike general-purpose computers, embedded systems are dedicated systems for specific applications. The goal is to make everything simpler, more convenient, more general, and more applicable; its hardware and software must be designed efficiently, tailored, and removed. Redundancy strives to achieve higher performance on the same silicon area.
The embedded system is mainly composed of embedded processor, peripheral hardware device, embedded operating system and specific application program. It is a stand-alone "device" that integrates software and hardware. It is used to implement other devices. Control, monitoring or management functions.
Embedded systems should have the characteristics of high reliability; in the harsh environment or sudden power failure, the system still needs to work normally; many embedded applications require real-time processing capabilities, which requires an embedded operating system ( EOS) has real-time processing capability; software code in embedded systems requires high quality and high reliability, and is generally solidified in read-only memory or flash memory, that is, software requires solid-state storage instead of storage on a disk. in.
2 The relationship between pervasive computing and wireless internet and network computing
When IBM proposed the concept of "ubiquitous computing", it was used to describe the era when personal computers are no longer at the core of innovation, and they are not intentionally called the wireless era. Because IBM sees the ability to compute, communicate, store, and process from traditional computers to a wide variety of devices. Today, we are only linking ubiquitous computing to mobile phones and PDAs, but computing is coming in different forms and experiences - it is constantly being loaded into air pumps, meters, appliances and clothing. For companies like IBM, “ubiquitous computing†is important because it has the same impact on infrastructure and front-end equipment. For business operations, “ubiquitous computing†will change the way companies communicate with their customers, suppliers and employees. Get more out of your e-commerce investment by reaching your customers and mobile work anytime, anywhere. More importantly, ubiquitous computing can reduce the complexity of equipment use and make our lives easier and more efficient for human beings surrounded by information.
In fact, ubiquitous computing is a natural extension of network computing, which allows not only PCs but also other small smart devices to be connected to the network, so that people can get information and take action on the fly. When this type of computing mode is widely adopted, people can use their favorite devices (mainly embedded system devices) in a consistent way to get information anytime, anywhere. The so-called "consistent approach" emphasizes the consistency of key information and key data, and its manifestation can be diversified, depending on factors such as user preferences and equipment.
3 Comparison between pervasive computing and traditional computing models
Pervasive computing is very different from traditional computing models, which puts new demands on the infrastructure that provides services. The traditional computing model is a two-tier structure: a system is designed for a certain device to suit the access and display of that particular device. At design time, the network protocol and display performance of that particular device must be designed.
Pervasive computing mode has great difficulty in realizing the connection of multiple application services to multiple smart devices, which makes it necessary to rewrite those application services for each additional device, and each additional service needs to rewrite those devices. s application. This limitation is determined by the hierarchy of existing systems. However, it is difficult to foresee what new, smart devices that users are happy to use in the future; and some devices can communicate in both directions, and some can only passively receive information in one direction. Existing systems are very complex when it comes to expanding support for new devices and new application services. For example, today we can use SMS (short message) and WAP mobile phones to access stock information. We can't foresee what tomorrow's popular devices are. Moreover, each person's personality varies from person to person, and the device preferences also want to be personalized, the future. The information equipment will be a group of people, and a hundred schools of thought contend.
Embedded computing not only requires fast and consistent network computing, but also requires the system to store its execution code and data in a “common†“small†space.
2 Robust law
Embedded computing not only requires a fast and efficient calculation of the system, but also requires that the system continue to operate normally in the event of an error in some computing units.
3 real-time law
The calculation results of the embedded system depend not only on the correctness of the logic operation of the system, but also on the calculation time of the operation result.
4 redundancy rule
After the embedded system has sufficient redundancy, the impact of the system's “initial sensitivity†on its “final calculation results†becomes minimal.
5 Structural rules
For embedded systems, the trend in structural complexity indicates:
a The simplest and more effective system structure (The simplest is the best);
b The more complex is more stable.
6 The law of simplicity
When simplifying an embedded system, the interaction between the remaining functions of the system becomes stronger and stronger;
When the functionality of the system is reduced, the probability of the success of the alien intruder becomes greater and greater.
7 Conservation Law
If you want to retain a system function in an embedded system, it is best to treat all other functions as "sacred and inviolable";
The function of the system is removed (extinct) or generated (invasive), which will definitely cause a major shift in the overall (cluster) structure and its dynamic performance.

8 Organizational rules
Embedded Internet The most important thing is not the characteristics of individual devices in the network, but the overall order that exists in the network, that is, the network order.
In a highly redundant network, the single role of the device can no longer constitute the main factor affecting the overall performance of the system, and all the nodes and their connected features play a major role.
9 Network rules
The nature of the network formed by a group of embedded Internet nodes interacting with a group of devices is often not significantly related to the nature of individual nodes.
10 message law
Guaranteed lookup messages: It has strict time-sensitive or basic normal system operation requirements, and such messages require a time guarantee from the system. That is, once activities or tasks caused by such messages are executed, their time limits must be guaranteed by the system during certain time intervals.
Best-effort message: It has a typical soft time limit, that is, its time limit is defined by the time series of the activity or the task itself, and its time-limited requirements can be met without system guarantee.
11 Principles of immunity
The embedded Internet's immune system should be a life-like mechanism. The immune function is a "feedforward" system, so the system should have the ability to foresee, so that it can be "small" poison attack (large) poison. .
12 Fusion Law
The embedded Internet is a complex network that parses complex network structures with simple “compositionsâ€, allowing the system to interpret “whole†from isolated “compositions†or to allow the system to express “global†from “nodesâ€. .
13 Cost-effectiveness rule
If System A is System B's embedded system, ie B(a), the cost of System A should not exceed 10% of System B's cost, and the cost of System B(a) should be greater than the sum of System A and System B costs. , the cost performance of system B (a) should be increased by 30%
British Switch Socket W86A Series
Screwfix Chrome Sockets,Polished Chrome Light Switch,Timer Outlet Plug,Electrical Sockets And Switches
Guangdong Jinli Electrical Appliance Co., Ltd , https://www.sokelectric.com
